Understanding Cybersecurity Risk Assessments
Hello, fellow business owners and leaders! In today’s digitally driven world, where data is the cornerstone of any organization’s success, the significance of cybersecurity cannot be emphasized enough. In an era where cyber threats continuously evolve, it’s critical to safeguard your business from potential data breaches, financial losses, and reputation damage. This is precisely where “cybersecurity risk assessments” come into play. In this blog, we’ll unravel the concept of cybersecurity risk assessments, highlighting their vital role in fortifying your business against digital threats.
Understanding Cybersecurity Risk Assessments
Let’s start by defining what a cybersecurity risk assessment entails. Picture it as a thorough checkup for your company’s digital health. It serves as a comprehensive evaluation of your organization’s vulnerabilities, potential threats, and the potential consequences of a cyberattack. Think of it as a diagnostic tool that allows you to identify weak points in your cybersecurity defenses.
Why Cybersecurity Risk Assessments Are Essential
Identifying Vulnerabilities: A risk assessment is your flashlight in the dark, revealing areas where your cybersecurity measures may be inadequate. These vulnerabilities can range from outdated software to weak passwords or unpatched systems. Once you’re aware of your weak spots, you can proactively strengthen them.
Prioritizing Security Measures: Not all security threats carry the same weight. A risk assessment helps you pinpoint which vulnerabilities pose the most significant risk to your business. This insight enables you to allocate your resources effectively, tackling the most critical issues first.
Meeting Compliance Requirements: Many industries and regulatory bodies mandate regular risk assessments as part of compliance. Neglecting these requirements can result in hefty fines and legal consequences.
Safeguarding Reputation: A data breach can mar your business’s reputation and erode customer trust. A risk assessment serves as a shield, minimizing the chances of a breach and preserving your brand’s image.
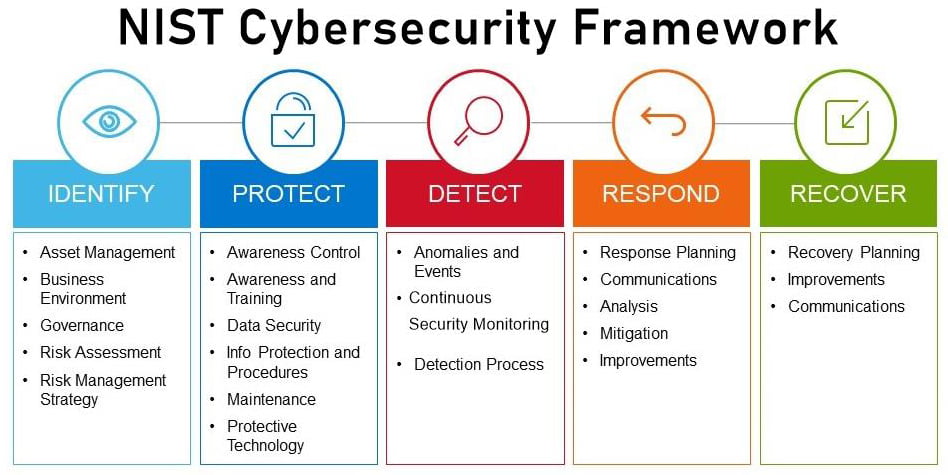
The Step-by-Step Process
A typical cybersecurity risk assessment consists of the following stages:
Asset Inventory: Begin by identifying and categorizing all digital assets, encompassing sensitive data, hardware, and software.
Threat Identification: Pinpoint potential threats, including malware, phishing attacks, or insider risks.
Vulnerability Assessment: Detect weaknesses in your systems, applications, and processes.
Risk Analysis: Assess the likelihood and potential impact of each threat exploiting your vulnerabilities.
Risk Mitigation: Develop a plan to mitigate risks, incorporating security measures and policies.
Monitoring and Review: Regularly revisit and update your cybersecurity strategy to stay ahead of evolving threats.
Choosing the Right Assessment Method
Various assessment methods cater to different facets of cybersecurity. Here are a few popular options:
Penetration Testing: Skilled ethical hackers attempt to exploit vulnerabilities to assess your defenses.
Security Audits: A comprehensive review of your security policies, procedures, and technical controls.
Vulnerability Scanning: Automated tools scan your systems for known vulnerabilities.
Security Questionnaires: Evaluate the security practices of third-party vendors if you rely on them for services.
Conclusion-
Cybersecurity Risk Assessments
In a digital landscape where cyber threats persistently evolve, cybersecurity risk assessments serve as your fortress against potential disasters. They provide valuable insights into your vulnerabilities, empowering you to take proactive steps to shield your business.
Investing in cybersecurity is not merely an option; it’s a necessity. By giving priority to cybersecurity risk assessments and acting upon their findings, you’ll be better equipped to safeguard your business against the ever-present cyber threats lurking in the digital realm.
Remember, it’s not a question of “if” a cyberattack will occur but “when.” Are you prepared?
Stay safe, stay secure, and fortify your business.
For additional cybersecurity insights and guidance, stay connected with us!


Todd Thanhauser is a dynamic technology consultant with over 30 years of experience in the technology space.
Todd is a former US Navy veteran and a musician who loves to travel the world.
When he’s not playing music or circling the globe Todd enjoys helping SMB’s leverage technology to it’s fullest
potential.
For information about all of our IT Support for Financial Services please visit our website Services Page.
Upper Echelon Technology Group, LLC is a premier technology provider.
For more information on our Cybersecurity Offerings and other offerings please visit www.uetechnology.net
Schedule a consultation or call us at 1-800-225-1392